In a stark reminder that the digital battlefield is constantly shifting, Google's Threat Analysis Group (TAG) has issued a sobering alert. A critical vulnerability in WinRAR, a compression tool installed on hundreds of millions of Windows desktops worldwide, has become a weapon of choice for sophisticated, state-backed hacking groups. The paradox is alarming: a flaw that was officially patched in July 2025 is now at the heart of "widespread" attacks by actors linked to global powers like Russia and China. For gamers who frequently download mods, custom maps, or repackaged titles from community forums, this alert is particularly critical—the very archives you trust could be a vehicle for a state-sponsored attack. This isn't a theoretical security bulletin; it's a live, ongoing cyber conflict exploiting a common utility.
The Vulnerability: CVE-2025-8088 Demystified
At its core, CVE-2025-8088 is a path traversal vulnerability within WinRAR's archive extraction process. In simple terms, this flaw allows a specially crafted RAR archive to trick the software into writing files to locations on a victim's computer where they should not be allowed to go, bypassing normal security restrictions.
The exploit's technical ingenuity lies in its abuse of a legacy Windows feature called Alternate Data Streams (ADS). This feature allows additional data to be attached to a file, like metadata, but it can be manipulated for malicious purposes. Attackers create RAR archives containing files with specially crafted ADS paths. When a user extracts this malicious archive with a vulnerable version of WinRAR, the software is deceived into writing the embedded payload—such as a malware executable—directly to a critical system location.
The most common and damaging destination is the Windows Startup folder. By dropping a malicious file here, attackers achieve immediate persistence: the malware automatically executes every time the system boots, ensuring their access remains even after a restart. The timeline of this exploit is particularly concerning. While RARLAB released the official fix in WinRAR version 7.13 on July 30, 2025, Google TAG observed active exploitation in the wild beginning July 18, 2025—nearly two weeks before the patch was available to the public, indicating highly advanced actors were ready to pounce.

The Actors: From Espionage to Cybercrime
The exploitation of CVE-2025-8088 reveals a diverse and dangerous threat landscape, uniting nation-state espionage with financially motivated crime.
On the state-sponsored front, Russian-linked groups have been particularly active. Google TAG tracks clusters of activity under identifiers like UNC4895 and APT44 (also known as Sandworm), groups historically tied to Russian military intelligence. These actors have weaponized the WinRAR flaw to target Ukrainian military and government entities, deploying sophisticated malware such as NESTPACKER and STOCKSTAY to establish long-term footholds for espionage and disruption.
Simultaneously, a separate China-linked threat actor has adopted the same exploit chain to deliver the POISONIVY remote access trojan (RAT), a powerful tool that provides attackers with complete backdoor control over infected systems.
Perhaps more telling of the flaw's danger is its rapid adoption by financially motivated cybercriminals. These groups have leveraged the exploit in attacks against the hospitality and travel sector in Latin America, financial institutions in Brazil, and various entities in Indonesia. This crossover from espionage to crime highlights the "commoditization" of the exploit. Shortly after its discovery, an actor using the moniker "zeroplayer" advertised the exploit code in underground cybercrime forums, effectively putting a powerful cyber-weapon up for sale to any paying criminal.

The Global Impact and the Gaming Community's Risk
Google's use of the term "widespread" is not hyperbolic. The attacks demonstrate how a single vulnerability in a ubiquitous piece of software can ripple across borders, sectors, and communities with devastating versatility.
The impact operates on two parallel levels, creating a uniquely pervasive threat. First, there is the geopolitical dimension, where the exploit serves as a digital spear for cyber-espionage in ongoing conflicts. Contrasting this is the global financial dimension, where cybercriminal groups, now armed with the same tool as nation-states, turn it against commercial enterprises for data theft and fraud. This dual use—from spycraft to street-level crime—exemplifies the modern threat landscape where advanced exploits become democratized dangers at a blistering pace.
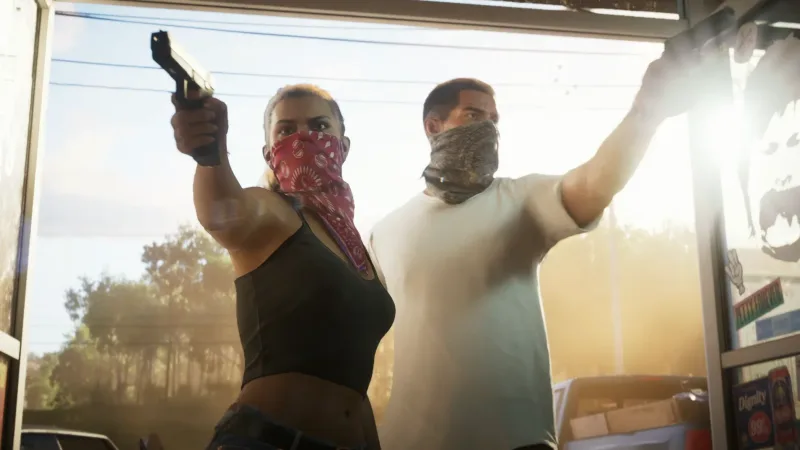
Why Gamers Are a Prime Target
This commoditization makes the gaming community a high-value target. Gamers are prolific downloaders, frequently acquiring mods, patches, repackaged games, and custom content from forums, unofficial sites, and peer-to-peer networks—often distributed as RAR archives. This trusted behavior creates a perfect attack vector. Furthermore, gaming PCs represent powerful hardware that can be hijacked for cryptomining or botnets, and gaming accounts themselves hold significant real-world value. The simplicity of the WinRAR attack vector—merely opening a malicious archive—makes every download a potential risk.
Defense and Mitigation: How to Protect Yourself
In the face of this widespread threat, decisive and immediate action is required. The primary, non-negotiable step for every user is to update WinRAR to version 7.13 or later. This update closes the path traversal flaw and is the only definitive way to prevent exploitation. The WinRAR update can be downloaded directly from the official RARLAB website.
For additional layers of detection, enabling security services like Google Safe Browsing can help warn users before they download known malicious archives containing this exploit.
Beyond patching, general security hygiene remains paramount:
- Exercise extreme caution with email attachments and archives downloaded from untrusted sources.
- Consider scanning downloaded archives with antivirus software before extraction.
- Maintain a strict policy of keeping all software, not just WinRAR, updated to the latest versions.
For organizations and gaming communities, the mandate is clearer. IT and security teams should immediately deploy the WinRAR patch across all managed endpoints. This incident also serves as a critical case study for user awareness training, emphasizing the dangers of unsolicited archives and the importance of applying software updates promptly.
CVE-2025-8088 has completed its dangerous transition from a listed vulnerability to an active tool in the arsenals of both nation-states and cybercriminals. Its journey from advanced actor exploit to commoditized crimeware in a matter of weeks illustrates the blistering pace of the modern threat landscape.
Gamers, take note: Before you open that next RAR file from a forum or unofficial site, verify your WinRAR is updated to version 7.13 or later. Better yet, consider using alternative, open-source archive tools like 7-Zip that were not affected by this specific flaw. This episode reinforces a fundamental principle of cybersecurity: the release of a patch is merely the beginning of the race. The finish line is crossed only when that patch is applied. In the ongoing conflict between defenders and a diverse array of attackers, vigilance—manifested as the prompt application of updates—remains the most critical defense.
Tags: WinRAR, Cybersecurity, CVE-2025-8088, State-Sponsored Hacking, Vulnerability Exploit, Gaming Security





Comments
Join the Conversation
Share your thoughts, ask questions, and connect with other community members.
No comments yet
Be the first to share your thoughts!