A new malware campaign is so stealthy it initially evaded every major antivirus engine. Its disguise? A critical Windows update. Its creators have specifically tailored the lure to look perfectly legitimate to one group of users, making it a particularly insidious threat.
Discovered by cybersecurity researchers at Malwarebytes, this sophisticated operation uses a convincing French-language support site to distribute what it claims is a "cumulative update" for a non-existent version of Windows. The campaign's danger lies in its blend of targeted social engineering and technical stealth; at the time of discovery, the core malicious payload had zero detections across 69 antivirus engines on VirusTotal. For gamers, whose accounts and digital inventories are high-value targets, this represents a clear and present danger, delivered in a disarmingly familiar package.
The Deceptive Lure: A Perfectly Crafted Fake
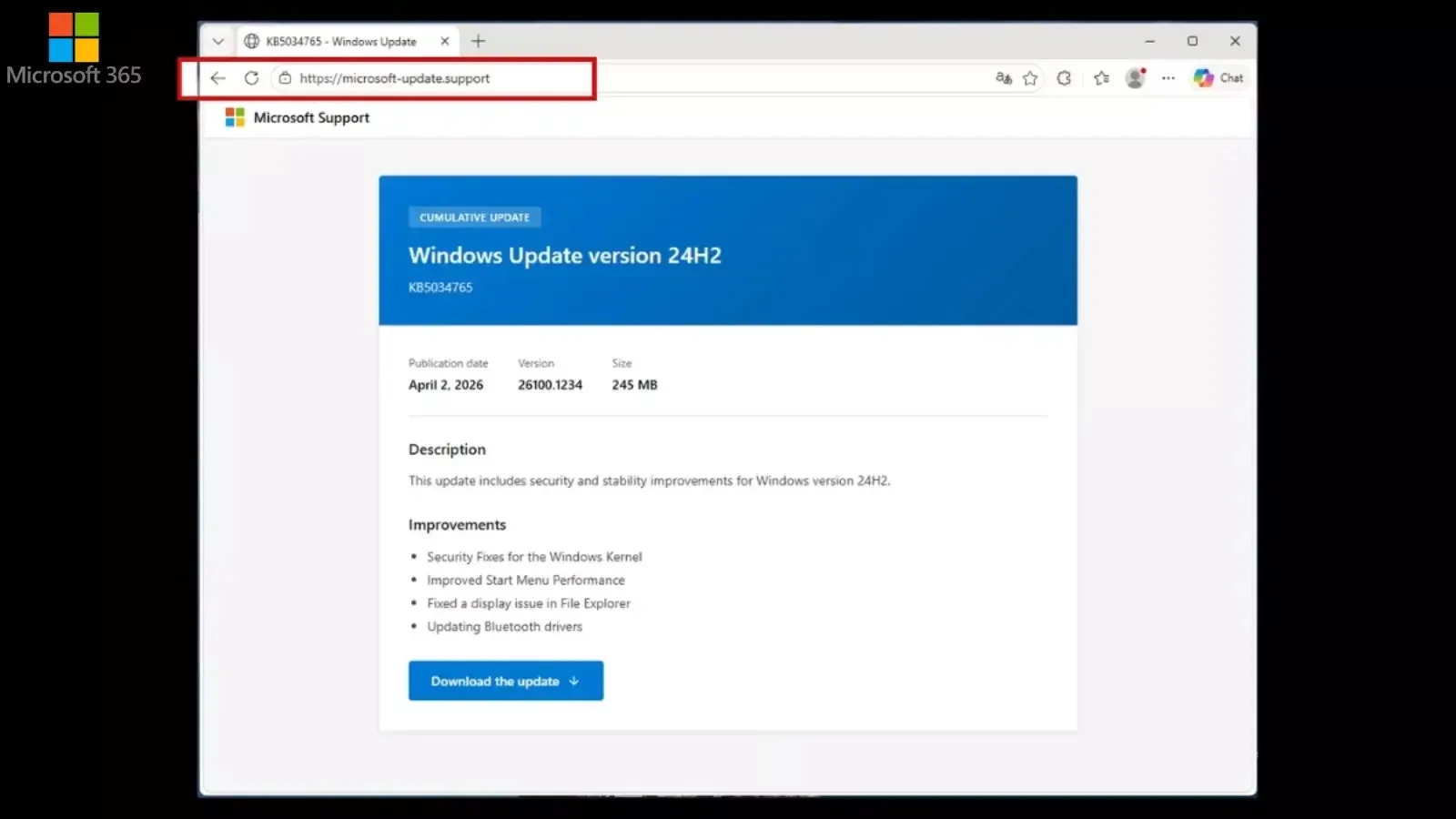
The campaign begins with a website designed for maximum local credibility. Hosted at the domain microsoft-update[.]support, the site is entirely in French, presenting itself as a Microsoft support page. Its central lure is a fake cumulative update for a fabricated "Windows version 24H2," complete with a plausible-sounding Knowledge Base (KB) article number to create a veneer of official legitimacy.
The offered download is an 83 MB Windows Installer package named WindowsUpdate 1.0.0.msi. To further sell the illusion, the file's properties are meticulously spoofed, listing "Microsoft" as the author. Perhaps most tellingly, the file carries a creation date stamp from the future—April 4, 2026—a tactic likely intended to confuse both users and automated security systems scanning for known malicious files.
Anatomy of Evasion: A Multi-Layered Threat
Once executed, the malware reveals its sophisticated, multi-layered architecture, engineered specifically to bypass security software. This defense evasion occurs in distinct stages:
- Layer 1: The Clean Shell. The initial executable,
WindowsUpdate.exe, is a legitimate, clean Electron application shell. To antivirus scanners, this first layer appears harmless, providing a safe entry point. - Layer 2: The Script Launcher. The Electron shell then executes a Visual Basic Script file named
AppLauncher.vbs. This script acts as a launcher for the next stage, a common technique to obscure the final payload. - Layer 3: The Malicious Interpreter. The VBS script launches a renamed Python 3.10 interpreter,
_winhost.exe. This interpreter is responsible for unpacking and executing the core malicious Python libraries, includingpycryptodome,psutil, andpywin32.
The critical finding from Malwarebytes was that this final, renamed Python executable (_winhost.exe) initially had zero detections on VirusTotal. This "zero-day" status for antivirus engines highlights the campaign's novelty and the significant stealth advantage it held in the early stages of its deployment.
The Malicious Payload: Data Theft and Persistence
The core functionality is contained within heavily obfuscated JavaScript files executed by the Python interpreter. The malware is a dedicated information stealer, designed to harvest a wide array of sensitive data from an infected system. Its primary targets include:
- Saved credentials from web browsers.
- Autofill payment information and credit card details.
- Session cookies and account tokens, with a specific module for stealing Discord tokens.
This is where the threat becomes acutely personal for gamers. Stolen browser credentials and session cookies are the primary keys used to hijack Steam, Epic Games, Xbox, and PlayStation accounts. A stolen Discord token can give an attacker full, undetected access to your gaming communications and communities, potentially leading to social engineering attacks on your friends or theft of valuable in-game items traded via chat.
To ensure it survives a system reboot, the malware establishes persistence through two primary methods. It creates a registry run key named SecurityHealth, a name chosen to mimic legitimate Windows security processes. It also places a deceptive shortcut file named Spotify.lnk in the user's Startup folder, ensuring the malware reactivates when the user logs in.
The malware also exhibits aggressive defensive behavior. Sandbox telemetry analyzed by researchers showed the process launching taskkill.exe over 200 times in a short period. This pattern is consistent with attempts to terminate security tools, analysis software, or even competing malware on the compromised system. It also performs victim fingerprinting by checking the public IP address and geolocation, likely for targeting or tracking purposes.
The Attack Chain: Communication and Data Exfiltration
The malware's network activity completes the attack chain. It communicates with a command-and-control (C2) server hosted on a Cloudflare Workers domain: sync-service.system-telemetry.workers[.]dev. The use of a legitimate service like Cloudflare Workers is another evasion tactic, as traffic to such domains often appears less suspicious than traffic to a dedicated malicious server.
The final destination for the stolen data is the file-sharing service store8.gofile[.]io. By exfiltrating credentials and sensitive information to a public file-hosting service, the attackers create a dead-drop that is difficult to trace back to them.
The campaign's specific targeting of French users is a strategic choice. By leveraging a localized lure and a French-language site, the attackers significantly increase the perceived legitimacy of the scam for that audience. Researchers speculate this may also be leveraging France's history of significant data breaches, where users could be more conditioned to seek out third-party support or updates, making them more vulnerable to such convincing fakes.
How to Protect Yourself: Verification and Best Practices
This campaign underscores a fundamental rule of PC security. The only legitimate sources for Windows updates are Settings > Windows Update on your PC or the official Microsoft Update Catalog website. Microsoft never distributes full update installers through third-party "support" sites.
To avoid falling victim to similar threats:
- Treat third-party "support" sites with extreme caution, especially those that prompt direct downloads of executables or installers.
- Keep your security software updated. Malwarebytes has since updated its detection databases to catch this specific threat, highlighting how vital updated definitions are.
- Be inherently skeptical of updates for non-existent, beta, or future software versions. If you haven't heard about a major new version through official channels, it almost certainly isn't real.
🔒 Key Takeaway for Gamers:
Your gaming accounts are lucrative targets. Protect them proactively:
- Use Unique Passwords: Never reuse passwords between your gaming platforms (Steam, Epic, etc.), Discord, and your email.
- Enable 2FA Everywhere: Two-factor authentication is the single most effective barrier against account takeover, even if your password is stolen.
- Verify Update Sources: Any prompt to download a "Windows update" outside of your PC's Settings menu is a major red flag.
This campaign, from its initially undetectable payload to its localized French lure, demonstrates that the most dangerous threats are those we're most likely to trust. For gamers, whose accounts and digital assets are high-value targets, the lesson is clear: your first move against any 'update' prompt should be to verify, not to click. The integrity of your gaming world depends directly on the security of your real-world system. While cyber threats will continue to evolve in complexity, your most powerful security tools remain disciplined verification and robust account hygiene.
Tags: Windows Security, Malware, Cyber Threat, Phishing, Data Theft, Gaming Security, Account Security




Comments
Join the Conversation
Share your thoughts, ask questions, and connect with other community members.
No comments yet
Be the first to share your thoughts!